Fun System Tool for Process Analysis and Debugging
By Andrius Miasnikovas
Over time I used quite an arsenal of various small utilities and tools for Windows that do some specific task. Some of them are outdated, no longer maintained, others I simply forgot because they were rarely used. One tool that I’ve been using for a while now is Process Explorer by Mark Russinovich who created many great tools to the Windows platform. If you don’t know this tool it’s a replacement for the Task Manager with many great features for monitoring processes, file handles, etc.
But today I want to share with you an alternative to Process Explorer called Process Hacker. At a glance it’s fairly similar to the Process Explorer but it has a few additional fun features like view GDI handles and inject DLL files. Another difference is when viewing the actual process you can see memory mappings, list of used modules and the handles of the process like files, registry keys, events, threads and others.
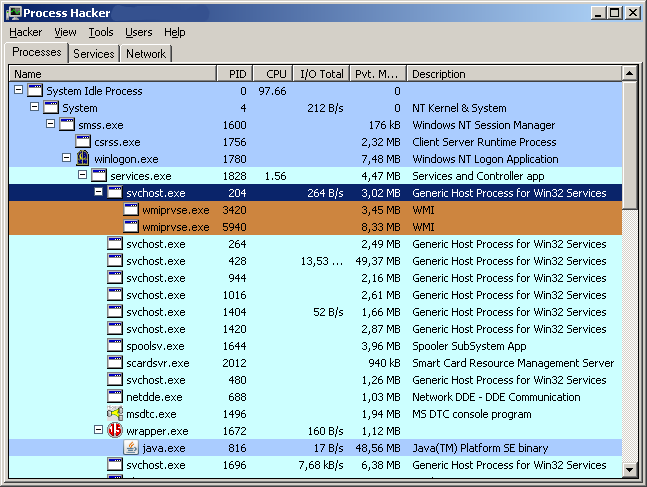
One feature that I liked is available from the Tools menu. You can easily create your own service from the binary of your choice. But be warned that not just any program can be used as a service. Talking about services you can get a nice overview of them with this tool. You can see all of the services that live on your system whether they’re running at the moment or not.
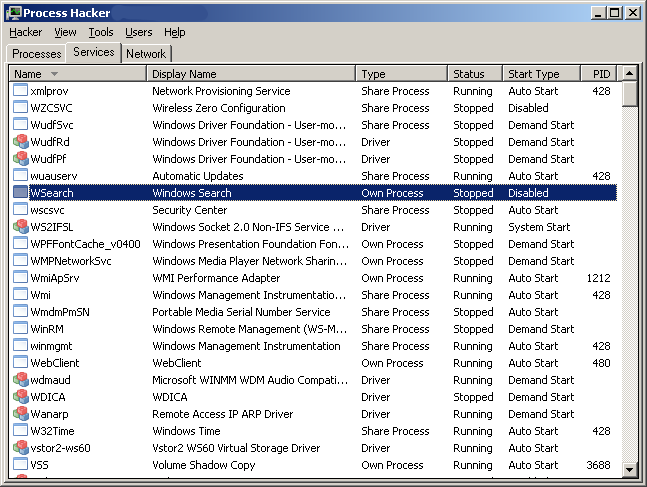
An interesting thing to note is that unlike the Windows service management console Process Hacker lets you see the driver services and even allows you to start or stop them as needed. Needless to say you could really mess up your system if you’re not careful. It will not prevent you from shooting yourself in the foot so make sure you know what you’re doing.
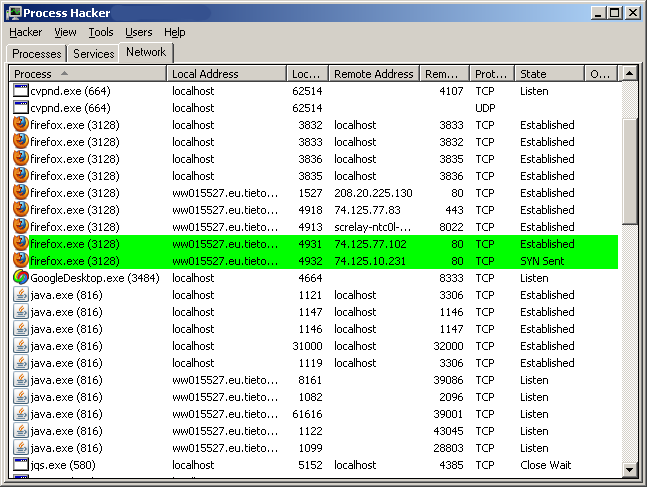
And let me quickly show you the third tab of Process Hacker which as the name suggests provide a list of network connections. This is somewhat similar to the command-line netstat utility only with a nicer interface. Also it tells you the name of the process that uses the network connection your interested in. It’s quite useful since at a glance you can tell what ports the application is communicating on be it TCP or UDP ports.
The binary package from sourceforge includes an additional utility called peview.exe which can be used for more static analysis of binary files. It provides you with the basic layout information about the binary file and presents you with a list of functions that are used by the binary and the list of functions that the binary exports for others to use.